-
Notifications
You must be signed in to change notification settings - Fork 0
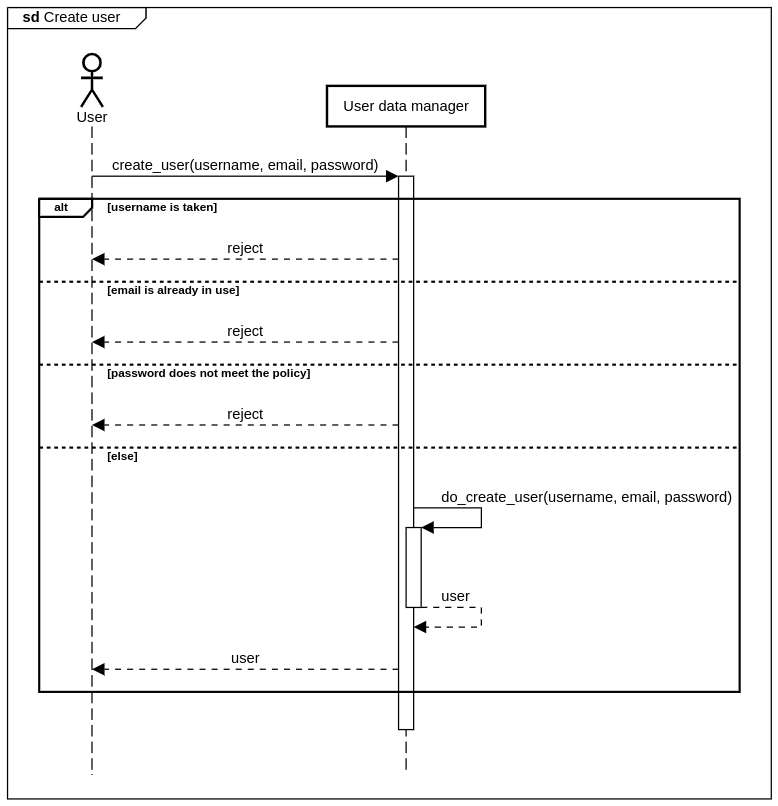
Behavioral Model of the System
We documented the behavioral model of our system in this document in the form of sequence diagrams. We created sequence diagrams based on the Structural Model of the System.
NOTE: To keep our diagrams simple, we omitted the calls to the database (data stores).
NOTE: To keep our diagrams simple, we omitted the calls to the log store. However, it should be assumed that all activity is logged properly.
NOTE: To keep our diagrams simple, we omitted the check whether the token the user presents is valid. However, it should be assumed that the user data manager performs this check when decodes the token, and if the token is invalid, rejects the request.
The user can create an account by choosing a username, and entering an email address and a password. The request is rejected if:
- The username is already taken
- The email is already used
- The password does not meet the policy
© Grotesque Gecko, 2020
- Functional Requirements and Use Cases
- Security Requirements and Objectives
- Threat Assessment
- Quality Gates
- Chosen Technologies
- Required Security Functionalities
- Structural Model of the System
- Behavioral Model of the System